I’ve been playing around with MicroPython and Home Assistant. MicroPython is a ‘bare-metal’-Python flavor that you can use to program ICs. Home Assistant is a home automation and home control software written in Python 3. It can be hosted on a Raspberry Pi. It enables you to connect a vast amount of different devices: lights, switches, sensors, locks etc.
This is a raw guide on how to make your own smart plug and connecting it to MQTT which is then connected to Home Assistant.
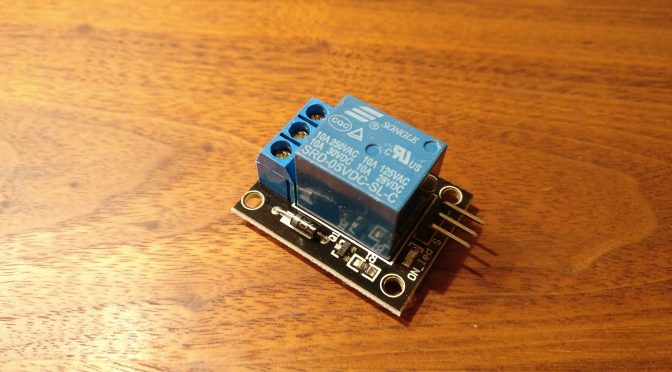
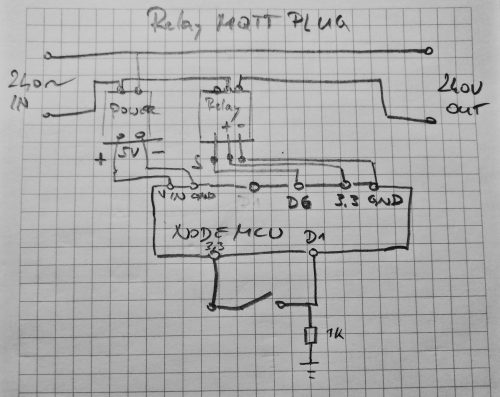
You will need a relay board (single relay), a NodeMCU board, a power adapter for 5V, a case, a button, some wire and a 1k resistor.
Connect the devices according to this schema (WARNING: Don’t do this if you’re not comfortable handling mains power!). Don’t forget earthing (it’s not on the diagram):
Flash the MicroPython firmware to the NodeMCU board. Put the ‘relay_mqtt.py‘ file on it as main.py. That way it will be run when the device boots up. Adjust the code to connect to your network and MQTT server first.
You can download the code here.
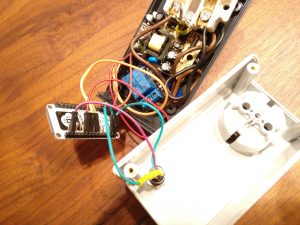
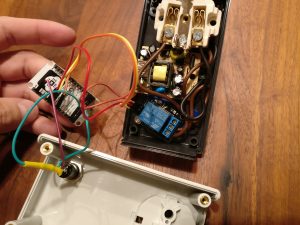
My device looks like this:
See the Home Assistant documentation for how to integrate the MQTT part with Home Assistant.
The nice thing is: you can press the button to switch the device. The status of the device will update via MQTT and Home Assistant gets a correct status update. You can of course switch the device from within Home Assistant as well.
Happy hacking!